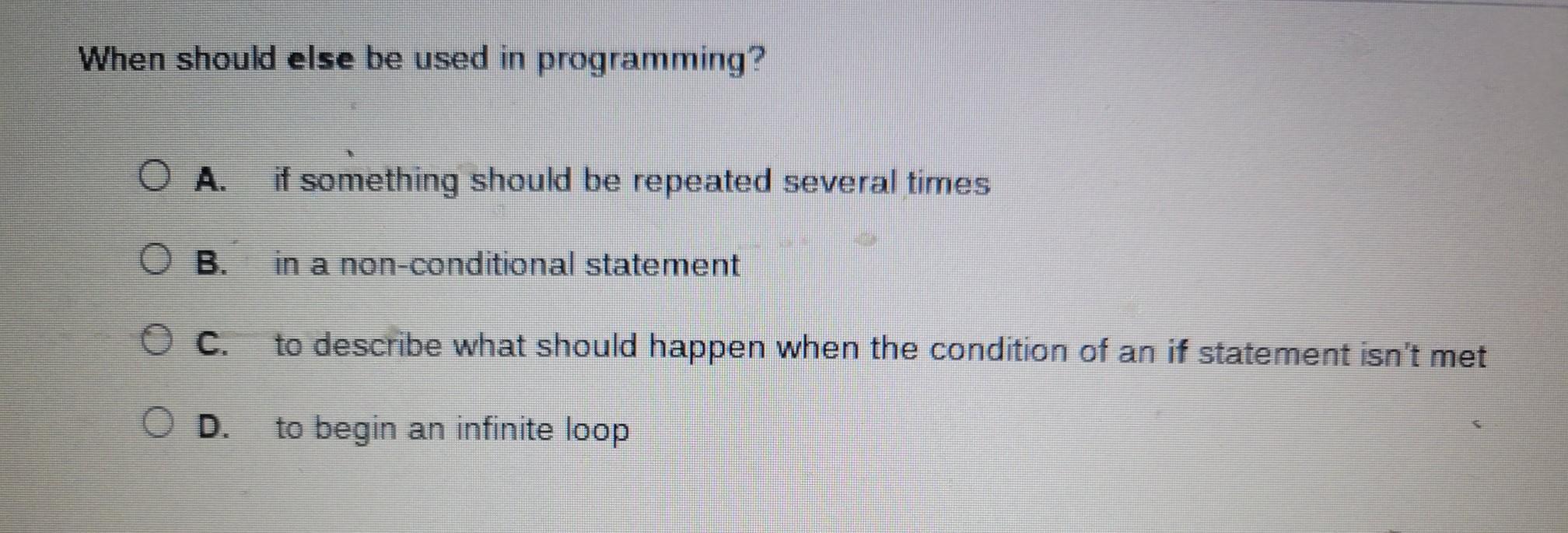
A. if something should be repeated several times
B. in a non-conditional statement
c. to describe what should happen when the condition of an if statement isn't met
D. to begin an infinite loop
Answers
Related Questions
problem 7-35 a satellite range prediction error has the standard normal distribution with mean 0 nm and standard deviation 1 nm. find the following probabilities for the prediction error:
Answers
A satellite range prediction error has the standard normal distribution with mean 0 nm and standard deviation 1 nm. We have to find the following probabilities for the prediction error.
Let X be the random variable that represents the satellite range prediction error with mean μ = 0 nm and standard deviation σ = 1 nm.
The probabilities for the prediction error are as follows:1) P(X > 1.1)
Let Z be the standard normal random variable, then z-score is given as:
z = (X - μ)/σ = (1.1 - 0)/1 = 1.1P(X > 1.1) = P(Z > 1.1)
We can find this probability from the standard normal table as:
P(Z > 1.1) = 0.1357Therefore, P(X > 1.1) = 0.1357.2) P(X < -1.6)
Similarly, let's find the z-score.z = (X - μ)/σ = (-1.6 - 0)/1 = -1.6P(X < -1.6) = P(Z < -1.6)
Using the standard normal table,P(Z < -1.6) = 0.0548
Therefore,
P(X < -1.6) = 0.0548.3) P(-1.96 < X < 1.96)
Using the standard normal table,
P(-1.96 < Z < 1.96) = 0.95Therefore, P(-1.96 < X < 1.96) = 0.95.4) P(|X| > 2)P(|X| > 2) = P(X < -2) + P(X > 2)
Let's find these probabilities separately using the standard normal table:
P(X < -2) = P(Z < -2) = 0.0228P(X > 2) = P(Z > 2) = 0.0228
Therefore,
P(|X| > 2) = P(X < -2) + P(X > 2) = 0.0228 + 0.0228 = 0.0456.
Thus, the probabilities for the prediction error are as follows
:1) P(X > 1.1) = 0.1357.2) P(X < -1.6) = 0.0548.3) P(-1.96 < X < 1.96) = 0.95.4) P(|X| > 2) = 0.0456.
To know more about range prediction visit:-
https://brainly.com/question/15401167
#SPJ11
auditing __________ the computer means inputs, outputs, and processing are checked.
Answers
Auditing around the computer system means inputs, outputs, and processing are checked.
1. Auditing refers to the systematic examination and evaluation of various components and activities within a computer system to ensure their accuracy, integrity, and compliance with established standards and controls.
2. Inputs in a computer system can include data, commands, and instructions that are provided to the system by users or other sources. During an audit, the inputs are checked to verify their authenticity, completeness, and accuracy.
3. Processing refers to the operations and manipulations performed on the inputs to generate the desired outputs. The audit examines the processing activities to ensure they are carried out correctly and in accordance with established procedures and controls.
4. Outputs, on the other hand, are the results or information generated by the computer system in response to the inputs and processing. Auditing the outputs involves comparing them to expected or desired outcomes, ensuring that they are correct, complete, and properly formatted.
By conducting a thorough audit of the computer system, organizations can identify and address potential errors, irregularities, or security breaches. It helps ensure the reliability and integrity of the system's operations, safeguards against data corruption or loss, and provides assurance that the system is functioning as intended.
To learn more about processing visit :
https://brainly.com/question/32113838
#SPJ11
4. problem 38 find the error due to the reference input. find the error due to the disturbance input. add the results (by superposition) to find the total error.
Answers
To find the total error in problem 38, we need to consider two types of errors: error due to the reference input and error due to the disturbance input. First, let's consider the error due to the reference input. This error occurs when the system is unable to track the desired output accurately.
To calculate this error, we assume that the disturbance input is zero and analyze the system's response to the reference input only. We can use the closed-loop transfer function of the system to find the error due to the reference input. Second, let's consider the error due to the disturbance input. This error occurs when external factors affect the system's output and cause it to deviate from the desired output. To calculate this error, we assume that the reference input is zero and analyze the system's response to the disturbance input only.
We can also use the closed-loop transfer function of the system to find the error due to the disturbance input. Once we have calculated the errors due to the reference and disturbance inputs separately, we can use the principle of superposition to find the total error. This principle states that the response of a linear system to a sum of inputs is equal to the sum of the responses of the system to each input individually. Therefore, we can add the errors due to the reference and disturbance inputs to find the total error. In summary, to find the total error in problem 38, we need to calculate the error due to the reference input, the error due to the disturbance input, and then add the results (by superposition) to find the total error. To find the total error in problem 38, we need to follow these steps: Find the error due to the reference input. This error occurs when the system is unable to track the desired output accurately. To calculate this error, we assume that the disturbance input is zero and analyze the system's response to the reference input only. We can use the closed-loop transfer function of the system to find the error due to the reference input. Second, let's consider the error due to the disturbance input. This error occurs when external factors affect the system's output and cause it to deviate from the desired output. To calculate this error, we assume that the reference input is zero and analyze the system's response to the disturbance input only. We can also use the closed-loop transfer function of the system to find the error due to the disturbance input. Once we have calculated the errors due to the reference and disturbance inputs separately, we can use the principle of superposition to find the total error. This principle states that the response of a linear system to a sum of inputs is equal to the sum of the responses of the system to each input individually. Find the error due to the disturbance input. Add the results (by superposition) to find the total error. Unfortunately, I cannot provide a specific answer without more information about the system and inputs. Please provide the necessary details, and I'll be happy to help you solve the problem.
To know more about errors visit:
https://brainly.com/question/30524252
#SPJ11
Which of the following is not an activity performed entirely within a CPU? Fetch instructions Perform Boolean operations Perform arithmetic operations Move data between registers
Answers
The activity which is not performed entirely within a CPU is "option A. Fetch instructions."
1.When a CPU executes instructions, the first step is to fetch the instructions from the memory. The CPU needs to access the memory subsystem to retrieve the instructions, as they are stored in the system's memory.
2. The memory subsystem consists of various components, including RAM (Random Access Memory) and cache, where instructions and data are stored. The CPU interacts with these components to fetch the instructions needed for execution.
3. The fetch instruction process involves the CPU sending a memory address to the memory subsystem to retrieve the instruction stored at that address. The memory subsystem then locates the instruction and transfers it back to the CPU.
4. The interaction between the CPU and the memory subsystem during the fetch instruction process relies on buses and memory controllers. Buses provide the pathways for data transfer between the CPU and memory, while memory controllers manage the communication and data transfer between the CPU and memory modules.
Therefore, fetching instructions requires the involvement of the memory subsystem, including accessing memory addresses, transferring data between memory and the CPU, and utilizing buses and memory controllers. Other tasks of performing arithmetic and boolean operations , moving data between registers are performed by CPU.
The correct question should be :
Which of the following is not an activity performed entirely within a CPU?
A. Fetch instructions
B. Perform Boolean operations
C. Perform arithmetic operations
D. Move data between registers
To learn more about CPU visit :
https://brainly.com/question/30751834
#SPJ11
Assignment details: For this assignment, students are required to investigate the following: 1. Learn more about IoT through secondary research over the internet. a. Write only 1 paragraph about what IoT is. 2. Research the internet about IoT applications in the Agriculture field. a. Write 2 paragraphs about how IoT helped Agritech industries. b. Write about 2 innovative ideas using IoT is Agritech (1 paragraph each) 3. Suggest new applications of IoT in any field.
Answers
The Internet of Things (IoT) is a network of interconnected devices that collect and exchange data through the Internet, enabling automation, monitoring, and control of various systems.
IoT has found significant applications in the agriculture sector, revolutionizing Agritech industries by enhancing efficiency, productivity, and sustainability. Additionally, there are innovative ideas using IoT in Agritech, such as precision agriculture and smart irrigation systems. Furthermore, IoT has the potential to be applied in various other fields, including healthcare, transportation, and smart cities.
IoT is a concept that refers to a network of interconnected devices, sensors, and systems that can communicate and exchange data with each other through the Internet. These devices can range from everyday objects to complex machinery and infrastructure. The data collected by IoT devices can be analyzed and used to automate processes, improve decision-making, and optimize efficiency in various domains.
In the agriculture field, IoT has significantly impacted Agritech industries. IoT applications have enabled smart farming practices, providing real-time monitoring and control of farming operations. Farmers can utilize IoT devices to monitor soil conditions, weather patterns, crop growth, and livestock health. This data-driven approach helps optimize resource usage, enhance crop yields, and reduce environmental impact. IoT has also facilitated precision agriculture techniques, such as targeted irrigation, fertilization, and pest management, leading to better crop quality and reduced costs.
Furthermore, innovative ideas using IoT in Agritech include precision agriculture and smart irrigation systems. Precision agriculture utilizes IoT sensors and data analytics to monitor and manage crops on a precise and individualized level. This enables farmers to optimize resource allocation, minimize waste, and maximize crop yield. Smart irrigation systems utilize IoT devices to monitor soil moisture levels and weather conditions, allowing for automated and efficient irrigation management. These systems ensure that crops receive the right amount of water, reducing water usage and minimizing water wastage.
Besides the agriculture field, IoT can be applied to various other domains. In healthcare, IoT can enable remote patient monitoring, smart medical devices, and real-time health data analysis. In transportation, IoT can be used for intelligent traffic management, vehicle tracking, and autonomous vehicle systems. In smart cities, IoT can facilitate efficient energy management, waste management, and infrastructure monitoring. The potential applications of IoT are vast and can revolutionize numerous industries by improving efficiency, sustainability, and quality of life.
Learn more about Internet of Things here:
https://brainly.com/question/29767247
#SPJ11
which items represent the united states’s main service exports?
Answers
It is important to note that the composition of service exports may vary over time and can be influenced by economic factors, global trends, and policy changes. The items mentioned above represent some of the main service exports of the United States, but the specific mix may change in response to various factors impacting the global economy.
The United States' main service exports include the following items:
1. Financial Services: The U.S. is a global hub for financial services, including banking, insurance, asset management, and investment services. These services are in high demand worldwide and contribute significantly to the country's service exports.
2. Professional and Business Services: This category includes a wide range of services such as legal services, consulting, accounting, advertising, and architectural services. The U.S. is known for its expertise in these areas, and many multinational companies seek American professional and business services.
3. Information Technology (IT) Services: The U.S. is a leader in IT services, including software development, computer programming, data processing, and IT consulting. American IT firms have a strong presence globally, and their services are exported to various countries.
4. Tourism and Travel Services: The U.S. attracts millions of tourists every year, contributing to a significant portion of its service exports. Travel-related services, including accommodation, transportation, food services, and entertainment, play a vital role in the economy.
5. Education Services: The U.S. is a popular destination for international students seeking high-quality education. Universities and educational institutions generate substantial revenue by enrolling students from abroad, offering various academic programs and services.
6. Healthcare and Medical Services: The United States is known for its advanced healthcare system and medical expertise. Medical services, including medical tourism, specialized treatments, and healthcare consulting, contribute to the country's service exports.
To know more about service ,visit:
https://brainly.com/question/1286522
#SPJ11
total quality management (tqm) programs are not concerned with
Answers
Total Quality Management (TQM) programs are concerned with every aspect of a business's operations and processes. There are no specific areas that TQM programs are not concerned with. TQM is a management philosophy that aims to improve customer satisfaction and loyalty by continuously improving all aspects of a business.
It involves a holistic approach to quality management, meaning that every aspect of the business is considered in order to ensure that the highest possible level of quality is achieved. TQM programs typically involve a range of strategies and techniques, including statistical process control, employee empowerment, and continuous improvement processes. TQM programs are designed to be all-encompassing and therefore are concerned with all aspects of a business's operations. This includes things like product design, production processes, customer service, marketing and sales, and supply chain management. TQM programs are also concerned with the culture and values of a business, as these can have a significant impact on the quality of products and services.
In summary, TQM programs are not concerned with any specific areas of a business's operations, as they aim to improve quality across the board. The goal of TQM is to create a culture of continuous improvement, where everyone in the organization is focused on delivering the highest quality products and services possible. Total Quality Management (TQM) is a comprehensive approach to quality management that seeks to improve all aspects of a business's operations. TQM programs are not concerned with any specific areas of a business, as they aim to improve quality across the board. The goal of TQM is to create a culture of continuous improvement, where everyone in the organization is focused on delivering the highest quality products and services possible. This requires a holistic approach to quality management, where all aspects of the business are considered in order to ensure that the highest possible level of quality is achieved.
To know more about programs visit :
https://brainly.com/question/30613605
#SPJ11
summarizer and opinion seeker are examples of _________ functions.
Answers
Summarizer and opinion seeker are examples of Text analysis functions. Text analysis involves the use of computational methods and techniques to extract useful information, insights, or patterns from textual data.
Text analysis function encompasses various tasks such as summarization, sentiment analysis, topic modeling, named entity recognition, and more.
A summarizer function analyzes a given text or document and generates a concise summary that captures the key points or main ideas. It condenses the information while preserving the essential meaning.
An opinion seeker function, on the other hand, focuses on extracting opinions, sentiment, or subjective information from text. It aims to determine the attitudes, emotions, or evaluations expressed in the text, allowing for sentiment analysis or opinion mining.
Both these functions contribute to text analysis by automating the process of extracting relevant information and gaining insights from textual data.
To learn more about opinion: https://brainly.com/question/25437634
#SPJ11
when acquiring software using a traditional (non-agile) mindset
Answers
When acquiring software using a traditional (non-agile) mindset, it is essential to determine functional requirements, non-functional requirements, and constraints.
Functional Requirements:
These requirements define the specific functionalities and features that the software must possess to meet the needs of the users and stakeholders. Functional requirements describe what the software should do and how it should behave in various scenarios. They outline the desired behavior, inputs, outputs, and interactions with users or other systems.Non-functional Requirements:
Non-functional requirements focus on the quality attributes and characteristics of the software, rather than its specific functionalities. These requirements address aspects such as performance, scalability, reliability, security, usability, and maintainability. Non-functional requirements define the criteria that the software must meet in terms of its performance, user experience, security measures, and other relevant factors.Constraints:
Constraints refer to any limitations or restrictions that impact the software development process or the final product. Constraints can be related to technology, budget, time, resources, regulatory compliance, or organizational policies. These constraints define the boundaries within which the software needs to be developed and deployed.Determining these requirements is essential in a traditional acquiring software approach because they provide a clear understanding of what needs to be delivered, both in terms of functionality and quality.
The question should be:
when acquiring software using a traditional (non-agile) mindset, which software requirements are best determined?
To learn more about software: https://brainly.com/question/28224061
#SPJ11
the creation of a unique advantage over competitors is referred as:____
Answers
The creation of a unique advantage over competitors is referred to as competitive advantage. It signifies the ability of a business to outperform its rivals by offering superior products, services, or value propositions to customers.
Competitive advantage can be achieved through various means, such as cost leadership (providing products at lower costs), differentiation (offering unique and desirable features), or focus (targeting specific market segments).
By creating advantage over competitors, it enables a business to attract and retain customers, command higher prices, achieve higher profit margins, and establish a strong market position.
Developing and sustaining a competitive advantage is crucial for long-term success and profitability in today's highly competitive business environment.
To learn more about advantage: https://brainly.com/question/26514848
#SPJ11
what proportion of patients in this sample with low hemoglobin levels presented with a subsequent malignancy? round to 2 decimal places.
Answers
To determine the proportion of patients with low hemoglobin levels who presented with a subsequent malignancy, follow these steps:
1. Identify the total number of patients with low hemoglobin levels.
2. Identify the number of patients with low hemoglobin levels who also presented with a subsequent malignancy.
3. Divide the number of patients with both low hemoglobin levels and subsequent malignancy by the total number of patients with low hemoglobin levels.
4. Multiply the result by 100 to convert it into a percentage.
5. Round the percentage to 2 decimal places.
Your answer: The proportion of patients in this sample with low hemoglobin levels who presented with a subsequent malignancy is XX.XX% (replace XX.XX with the calculated percentage after following the steps).
To know more about hemoglobin visit:-
https://brainly.com/question/29574129
#SPJ11
what step in the control process includes a definition of out of control
Answers
The step in the control process that includes a definition of out of control is the evaluation step. The evaluation step is where performance is measured and compared to the standards that were established during the planning phase. This is where managers identify whether or not the process is out of control.
In order to do this, they need to have a clear definition of what it means for a process to be out of control. This definition will typically be based on statistical analysis of past performance data, and will set limits on what is considered acceptable or unacceptable performance. The evaluation step is critical for ensuring that processes are functioning as intended. If a process is out of control, it means that it is not performing at the level that was expected.
This can be due to a variety of factors, such as changes in the environment, equipment failure, or human error. By having a clear definition of what it means for a process to be out of control, managers can quickly identify when problems arise and take corrective action to bring the process back into line. Without this definition, it can be difficult to identify when a process is out of control, and this can lead to delays, increased costs, and other problems.
To know more about control process visit :
https://brainly.com/question/32497289
#SPJ11
Note: In Computer science field specifically in data design and analysis.
Discuss any two types of information gathering techniques.
Answers
In the field of data design and analysis, two types of information-gathering techniques are surveys/questionnaires and interviews.
Surveys/questionnaires involve collecting data through standardized sets of questions, while interviews involve direct conversations to gather detailed and qualitative information.
Surveys/Questionnaires: Surveys and questionnaires are widely used information gathering techniques in data design and analysis. They involve presenting a standardized set of questions to a targeted group of respondents. Surveys can be conducted through various methods, including online platforms, paper-based forms, or telephone interviews. Surveys are efficient in collecting quantitative data and large sample sizes, allowing for statistical analysis and generalization of findings. They are useful for collecting data on opinions, preferences, behaviors, or demographic information. However, surveys may have limitations, such as response bias, limited opportunity for clarification, and the need for careful question design to ensure clarity and accuracy of responses.
Interviews: Interviews involve direct conversations between the researcher and the respondent to gather detailed and qualitative information. They provide an opportunity to explore complex topics, gather rich insights, and capture the nuances of individual perspectives. interview can be conducted in person, over the phone, or through video conferencing. They allow for probing and follow-up questions to delve deeper into the respondent's experiences, thoughts, and motivations. Interviews are particularly valuable when studying complex phenomena or when a deep understanding of the subject matter is required. However, interviews can be time-consuming, resource-intensive, and may be subject to interviewer bias. Careful planning and skilled interviewing techniques are necessary to ensure reliable and valid data collection.
Both surveys/questionnaires and interviews play important roles in information gathering for data design and analysis. They offer distinct advantages and considerations, and the choice between them depends on the research objectives, available resources, and the depth of insights required.
Learn more about information-gathering techniques here:
https://brainly.com/question/15289104
#SPJ11
Search engines consider a variety of factors when assigning a
rank (i.e., a position) to a website. Please name one of
those factors.
Answers
One important factor that search engines consider when assigning a rank to a website is the "relevance of its content" to the user's search query.
1. Search engines aim to provide the most relevant and useful results to users, so they analyze the content of web pages to determine their relevance to specific search terms or topics.
2. When a user enters a search query, search engines examine the content of web pages to identify those that are most likely to satisfy the user's intent. They analyze factors such as the presence and placement of keywords, the overall topic of the page, and the quality and comprehensiveness of the information provided.
3. To determine relevance, search engines employ sophisticated algorithms that evaluate various on-page and off-page factors. On-page factors include the presence and frequency of keywords in the page's title, headings, and body content.
4. Off-page factors, such as the number and quality of incoming links from other websites, also contribute to a page's relevance. These links act as "votes" of confidence from other sites, indicating that the linked page is considered valuable and trustworthy.
In summary, search engines consider the relevance of a website's content to a user's search query as a critical factor in determining its rank. By analyzing on-page and off-page factors, search engines strive to deliver the most relevant and useful results to users, improving their overall search experience.
To learn more about search engine visit :
https://brainly.com/question/32419720
#SPJ11
Is technology altering cultural behavior? How has it
influenced you?
Answers
Technology is altering cultural behavior by shaping the way we communicate, consume information, and interact with the world.
Its influence can be seen in various aspects of daily life, including social interactions, work habits, and entertainment choices.
Technology has significantly impacted cultural behavior in numerous ways. Firstly, it has transformed communication patterns, with the rise of smartphones, social media platforms, and instant messaging apps. People now rely more on digital channels for social interactions, which has both positive and negative consequences. It has enhanced connectivity, enabling people to stay connected across distances and facilitating the sharing of ideas and information. However, it has also led to concerns about reduced face-to-face interactions, increased screen time, and the impact on personal relationships.
Additionally, technology has revolutionized the way we consume information. With the advent of the internet and digital media, we have access to a vast amount of information at our fingertips. This has altered how we seek and process information, with a shift towards online sources, personalized content, and shorter attention spans. It has also influenced entertainment choices, with streaming services, online gaming, and social media platforms becoming prominent forms of leisure activities.
Personally, technology has influenced me in several ways. It has made communication more convenient and efficient, allowing me to stay connected with friends and family across the globe. It has also expanded my access to knowledge and resources, enabling self-learning and exploration of various topics. However, I am mindful of the potential drawbacks, such as the need for digital balance, privacy concerns, and the importance of maintaining offline connections.
In conclusion, technology is indeed altering cultural behavior by transforming communication, information consumption, and entertainment choices. Its impact varies across individuals and communities, and it is crucial to be aware of both the benefits and challenges it brings to our cultural landscape.
Learn more about Technology here:
https://brainly.com/question/30394733
#SPJ11
Show that we can solve the telescope scheduling problem in O(n) time even if the list of n observation requests is not given to us in sorted order, provided that start and finish times are given as integer indices in the range from 1 to n2.
Answers
In order to show that the telescope scheduling problem can be solved in O(n) time even when the list of n observation requests is not given to us in sorted order, we have to use a greedy approach. Sort the observation requests by their finish times in increasing order. Let us call this sorted list L.
The finish time is the time at which the observation request is completed. We can use any sorting algorithm like quick sort, merge sort, etc. The time complexity of sorting is O(nlogn) but since we have n2 observations, the time complexity of sorting is O(n2logn2) which is equal to O(n2logn).Step 2: Initialize the schedule list S as empty. We will use this list to keep track of the observations that have been scheduled.Step 3: For each observation request in L, do the following:If the observation request can be scheduled without overlapping with the observations already scheduled in S, then add it to the schedule list S and mark it as scheduled.Else, ignore the observation request since it cannot be scheduled without overlapping with the observations already scheduled in S.
The time complexity of this step is O(n) since we have n observation requests and each observation request takes constant time to process.Step 4: The schedule list S now contains the set of non-overlapping observations that can be scheduled. The time complexity of this step is O(n) since we have to iterate over the schedule list S to check if an observation request can be scheduled without overlapping with the observations already scheduled in S.The total time complexity of the algorithm is O(n2logn) + O(n) + O(n) = O(n2logn). However, since n2 is an upper bound on the integer indices of start and finish times, we can use a bucket sort algorithm to sort the observation requests in O(n) time. The time complexity of the algorithm now becomes O(n) + O(n) + O(n) = O(n). Therefore, we can solve the telescope scheduling problem in O(n) time even if the list of n observation requests is not given to us in sorted order, provided that start and finish times are given as integer indices in the range from 1 to n2.
To know more about telescope visit :
https://brainly.com/question/1915278
#SPJ11
The is_palindrome function checks if a string is a palindrome. A palindrome is a string that can be equally read from left to right or right to left, omitting blank spaces, and ignoring capitalization. Examples of palindromes are words like kayak and radar, and phrases like "Never Odd or Even". Fill in the blanks in this function to return True if the passed string is a palindrome, False if not.
def is_palindrome(input_string):
# We'll create two strings, to compare them
new_string = input_string.replace(" ", "").lower()
reverse_string = input_string.replace(" ",""). lower()[::-1]
if new_string == reverse_string:
return True
return False
----------------------------
print(is_palindrome("Never Odd or Even")) # Should be True
print(is_palindrome("abc")) # Should be False
print(is_palindrome("kayak")) # Should be True
Answers
The given code already checks whether the passed string is a palindrome or not. It first removes all the blank spaces from the input string using the replace() function and converts it into lowercase using lower() function.
Then, it creates a reversed string using slicing with [::-1] and compares it with the original string. If they are the same, it returns True, otherwise False. The given function named is_palindrome(input_string) takes one parameter, which is the input string that needs to be checked for being a palindrome or not. A palindrome is a string that can be read the same way from both ends, and this function checks for the same by comparing the input string with its reverse string.
To compare both strings, the function first removes all the blank spaces from the input string using the replace() function. Then, it converts both the input string and the reversed string into lowercase using lower() function, so that case doesn't affect the comparison. Finally, it creates the reversed string using slicing with [::-1]. This slicing operation means that it starts at the last character of the string and moves backwards towards the first character, with a step size of -1, thus reversing the string.
After creating both the strings, the function compares them using the equality operator (==). If both the strings are the same, it means that the input string is a palindrome, and the function returns True. Otherwise, if they are not equal, it returns False, indicating that the input string is not a palindrome. The function is then tested with three examples: "Never Odd or Even", "abc", and "kayak". The first example is a palindrome and should return True. The second example is not a palindrome and should return False. The third example is a palindrome and should return True as well.
To know more about palindrome visit:
https://brainly.com/question/13556227
#SPJ11
the standard enthalpy of formation for glucose [c6h12o6(s)] is −1273.3 kj/mol . what is the correct formation equation corresponding to this δhof ?
Answers
The correct formation equation corresponding to the standard enthalpy of formation for glucose [C6H12O6(s)] of −1273.3 kJ/mol is: C6H12O6(s) + 6O2(g) → 6CO2(g) + 6H2O(l) This equation shows that glucose is formed from its constituent elements (carbon, hydrogen, and oxygen).
In their standard states (solid carbon, diatomic oxygen gas, and liquid water) with a release of 1273.3 kJ/mol of energy. To determine the correct formation equation corresponding to the standard enthalpy of formation (ΔHf) for glucose [C6H12O6(s)], which is -1273.3 kJ/mol, you can follow these steps: Identify the elements and their standard states: carbon (C, solid graphite), hydrogen (H2, gas), and oxygen (O2, gas).
Write down the stoichiometry for the formation of one mole of glucose: 6 moles of carbon, 6 moles of hydrogen gas, and 3 moles of oxygen gas. Combine the elements in their standard states with the correct stoichiometry to form one mole of glucose. The correct formation equation corresponding to the standard enthalpy of formation for glucose is: 6C(graphite) + 6H2(g) + 3O2(g) → C6H12O6(s); ΔHf = -1273.3 kJ/mol
To know more about equation visit :
https://brainly.com/question/29657983
#SPJ11
the demand curve for froot loops breakfast cereal is very elastic because:
Answers
The demand curve for Froot Loops breakfast cereal is very elastic because it has a lot of substitutes. A product with an elastic demand has a lot of substitutes.
Customers can quickly and easily switch to other products if the price of Froot Loops breakfast cereal rises too much. Elastic demand is when the product's price affects demand. Consumers will react to changes in price. A price increase will result in a decrease in quantity demanded.
This means that an increase in price will result in a proportionately larger decrease in quantity demanded. The opposite is also true. A change in price for a product with elastic demand causes a substantial change in the amount of that product that customers purchase.
As a result, the total revenue of producers will change in the opposite direction of the price. If the price of a product with elastic demand rises, revenue will decrease. If the price of a product with elastic demand decreases, revenue will increase.
Substitutes for Froot Loops breakfast cereal can be considered as Cocoa Puffs, Cinnamon Toast Crunch, Lucky Charms, etc. The demand for Froot Loops breakfast cereal is elastic because if the price of Froot Loops cereal rises, consumers will switch to these other cereals as alternatives instead of paying more for Froot Loops.
To learn more about demand curve: https://brainly.com/question/1139186
#SPJ11
in outer space rock 1 with mass 5 kg and velocity <3500, -3000, 3600> m/s, struck rock 2, which was at rest. after the collision, rock 1's velocity is <3200, -2500, 3900> m/s.
Answers
Given,Mass of rock 1, m1= 5 kgVelocity of rock 1 before collision, v1i= <3500, -3000, 3600> m/sVelocity of rock 1 after collision, v1f= <3200, -2500, 3900> m/sMass of rock 2, m2= unknownVelocity of rock 2 before collision, v2i= 0 m/sVelocity of rock 2 after collision, v2f= unknownAs .
we can write:p1i = p1f + p2fwhere,p = mvHere,m = massv = velocityNow, let's calculate the momentum before collision:P1i = m1 × v1iP1i = 5 kg × <3500, -3000, 3600> m/sP1i = <17500, -15000, 18000> kg m/sNow, let's calculate the momentum after collision:P1f = m1 × v1fP1f = 5 kg × <3200, -2500, 3900> m/sP1f = <16000, -12500, 19500> kg m/sUsing the above equations;p1i = p1f + p2fp1i - p1f = p2f<17500, -15000, 18000> - <16000, -12500, 19500> = p2f<1500, -2500, -1500> = p2fNow, let's calculate the mass of rock 2:m2 = p2f / vm2 = <1500, -2500, -1500> / <0, 0, 0>m2 = undefinedTherefore, the long answer to the problem is as follows:The given question is related to the collision of two objects in outer space. When rock 1 with a mass of 5 kg and velocity <3500, -3000, 3600> m/s, struck rock 2 which was at rest, then the momentum of both the objects before collision and after collision would be equal to each other. Therefore,
the momentum before the collision can be calculated as P1i = m1 × v1i = 5 kg × <3500, -3000, 3600> m/s = <17500, -15000, 18000> kg m/s, and the momentum after collision can be calculated as P1f = m1 × v1f = 5 kg × <3200, -2500, 3900> m/s = <16000, -12500, 19500> kg m/s.Using the conservation of momentum, we can write;p1i = p1f + p2fwhere,p = mvHere, p1i is the momentum before collision, p1f is the momentum after collision of rock 1, p2f is the momentum after collision of rock 2, m is the mass, and v is the velocity.Therefore, p1i - p1f = p2f<17500, -15000, 18000> - <16000, -12500, 19500> = p2f<1500, -2500, -1500> = p2fNow, let's calculate the mass of rock 2;m2 = p2f / vm2 = <1500, -2500, -1500> / <0, 0, 0>m2 = undefinedTherefore, we can say that the mass of rock 2 is undefined.
To know more about sVelocity visit:
https://brainly.com/question/31013080
#SPJ11
the programmer must ensure that a recursive function does not become:____
Answers
The programmer's responsibility is to prevent a recursive function from becoming infinite by defining and implementing appropriate base cases.
A recursive function is a function that calls itself during its execution. It is a powerful programming technique used to solve problems that can be divided into smaller, similar subproblems. However, if not properly controlled, a recursive function can lead to an infinite loop, where the function calls itself indefinitely and never reaches a base case or termination condition.
To prevent a recursive function from becoming infinite, the programmer must carefully design and implement the function by ensuring that it progresses towards a base case. The base case is a condition that, when met, allows the function to stop calling itself and return a result. Without a proper base case, the recursive function will continue calling itself indefinitely, consuming system resources and potentially causing a stack overflow or crashing the program.
There are no specific calculations involved in preventing a recursive function from becoming infinite. It requires thoughtful programming and logical design to establish appropriate base cases and termination conditions.
By ensuring that the function reaches a base case and terminates eventually, the programmer can control the recursion and prevent excessive resource usage or program crashes. Proper design and careful consideration of the termination conditions are crucial to creating efficient and effective recursive functions.
To know more about Recursive Function, visit
https://brainly.com/question/30857989
#SPJ11
Briefly, explain the specific functional elements involved in a global logistics process; global networks for shippers and carriers; INCOterms; and critical importance of cargo insurance and liability in global transactions.
Answers
The global logistics process involves various functional elements such as transportation, warehousing, inventory management, and customs compliance. It relies on global networks for shippers and carriers to facilitate the movement of goods.
INCO terms are internationally recognized trade terms that define the responsibilities and obligations of buyers and sellers in global transactions. Cargo insurance and liability are of critical importance in global transactions to protect against loss, damage, or liability during the transportation of goods.
The global logistics process encompasses several functional elements that are essential for the movement of goods across international borders. These elements include transportation, which involves selecting the appropriate mode of transport (such as air, sea, or land) and managing the transportation logistics. Warehousing plays a crucial role in global logistics by providing storage facilities for goods before they are shipped or distributed. Inventory management ensures the availability of goods at the right time and in the right quantity. Customs compliance is vital to ensure that goods comply with customs regulations and requirements in different countries.
Global networks for shippers and carriers are essential for coordinating and managing logistics operations. These networks connect various parties involved in the supply chain, including manufacturers, suppliers, freight forwarders, and transportation providers. They enable efficient communication, collaboration, and tracking of shipments throughout the logistics process.
Incoterms, short for International Commercial Terms, are internationally recognized trade terms that define the obligations, costs, and risks associated with the transportation and delivery of goods. They provide a standardized framework for buyers and sellers to clarify their responsibilities in global transactions.
Cargo insurance and liability are critical aspects of global transactions. Cargo insurance protects against loss, damage, or theft of goods during transportation. It provides financial coverage to compensate for any potential losses. Liability refers to the legal responsibility and potential financial obligations of parties involved in the transportation of goods. Ensuring appropriate cargo insurance and understanding liability issues is crucial to mitigate risks and protect the interests of all parties involved in global transactions.
In summary, the global logistics process involves functional elements such as transportation, warehousing, inventory management, and customs compliance. Global networks facilitate coordination between shippers and carriers. INCOterms define the responsibilities of buyers and sellers in global transactions, and cargo insurance and liability play a vital role in protecting against potential losses and liabilities in the transportation of goods.
Learn more about global logistics here:
https://brainly.com/question/5186018
#SPJ11
which of the following does not determine a cpu's processing power?
Answers
The size of the computer case does not determine a CPU's processing power. A CPU's processing power is determined by several factors such as clock speed, number of cores, cache size, and the manufacturing process used to create the chip.
Clock speed is the rate at which a CPU can execute instructions, while the number of cores determines the number of tasks a CPU can handle simultaneously. Cache size is the amount of memory built into the CPU that it can use to quickly access frequently used data. The manufacturing process used to create the chip affects its efficiency and power consumption. The size of the computer case is not related to a CPU's processing power.
The size of the computer case is determined by the type of components used in the computer and the form factor of the motherboard. It does not affect the performance of the CPU or other components in the computer. Therefore, the size of the computer case is not a factor in determining a CPU's processing power.
To know more about CPU's processing power visit :
https://brainly.com/question/31332201
#SPJ11
13. do your tags support the option of writing a random id to the tag on every checkout, with the library database retaining a map of the random id to the item's number?
Answers
However, in general, it is possible to generate random IDs for tags and map them to items in a database. This process is commonly used in inventory management systems, where unique IDs are assigned to each item to track their movement and location.
In order to implement a system where random IDs are assigned to tags on every checkout, you will need to have a robust inventory management system in place. This system should be able to generate unique IDs, track the movement of items, and update the database with the latest information. The process of assigning random IDs to tags can be done using different techniques. One common method is to use RFID (Radio Frequency Identification) technology, where a unique code is embedded into each tag. This code can be read by a scanner, which then maps it to the item in the database.
Another approach is to use barcodes, which can also be generated randomly. Barcodes can be scanned using a barcode scanner, and the corresponding item information can be retrieved from the database. Regardless of the technology used, it is important to ensure that the mapping between the random ID and the item's number is accurate and up-to-date. This can be achieved by maintaining a robust inventory management system that tracks the movement of items and updates the database accordingly. In summary, it is possible to implement a system where random IDs are assigned to tags on every checkout, and the mapping between the ID and the item's number is maintained in a database. This requires a robust inventory management system and the use of technology such as RFID or barcodes to generate unique IDs. The accuracy of the mapping can be ensured by tracking the movement of items and updating the database in real-time.
To know more about unique IDs visit :
https://brainly.com/question/14391866
#SPJ11
laser technology used in surgical procedures is an example of technological advances in:
Answers
The laser technology used in surgical procedures is an example of technological advances in the medical field.
A laser is a device that emits light via a process of optical amplification based on the stimulated emission of electromagnetic radiation. The word "laser" is an acronym for "light amplification by stimulated emission of radiation."
Laser technology is used in various applications in modern society, including scientific research, manufacturing, medicine, and telecommunications.
Laser technology has revolutionized the medical industry, particularly in the area of surgical procedures. The precision and accuracy of lasers have enabled surgeons to perform surgeries with significantly fewer complications, less pain, and a shorter recovery time.
Laser surgery, also known as laser-assisted surgery, is a type of minimally invasive surgery that uses a laser beam to make incisions or remove tissues.
The laser beam is highly concentrated, which allows for a more precise cut than traditional surgical tools. Laser surgery is used in various procedures, including eye surgery, skin resurfacing, cancer treatment, and cosmetic surgery.
To learn more about laser: https://brainly.com/question/24354666
#SPJ11
using a computer screen with poor resolution or glare problems could cause which problem?
Answers
Using a computer screen with poor resolution or glare problems could cause eye strain or eye fatigue.
Eye strain:
Eye strain is a very common condition in which eyes feel exhausted, and it can be caused by using a computer screen with poor resolution or glare problems.Using computer screens for an extended period, reading, driving, watching television, or anything else that involves intense use of eyes for an extended period can cause eye strain.Symptoms of eye strain:
The symptoms of eye strain include headache, blurred vision, dry eyes, redness in eyes, double vision, difficulty in concentrating, neck, shoulder, and back pain. If the individual is suffering from eye strain, they can try taking breaks and blink their eyes frequently to avoid eye fatigue and reduce strain on the eyes.Additionally, it is always suggested to take an eye exam from an ophthalmologist to detect any underlying issue or weakness in the eyes.
To learn more about computer screen: https://brainly.com/question/9017156
#SPJ11
what contains information on how hard drive partitions are organized?
Answers
The hard drive's partitioning information is typically stored in a data structure called the partition table. The partition table contains entries that describe the size, location, and file system type of each partition on the hard drive.
The partition table resides in the Master Boot Record (MBR) or the GUID Partition Table (GPT) depending on the partitioning scheme used. It provides the necessary information for the operating system to identify and access the different partitions.
The partition table is essential for organizing and managing multiple partitions on a hard drive, allowing for efficient storage allocation and facilitating the organization of data and file systems within each partition.
To learn more about hard drive: https://brainly.com/question/28098091
#SPJ11
Which of the following commands lets you display a label on multiple lines within a cell O Split O Merge & Center o Wrap Text O Format Painter (50 of 50) In the function =SUM(B2:B6), which part of the function is the argument? e SUM O B2 O B6 B2:B6
Answers
The command that lets you display a label on multiple lines within a cell is "option C. Wrap Text."
In the function "=SUM(B2:B6)", the argument of the function is "option D. B2:B6."
1. The "Wrap Text" command in spreadsheet software, such as Microsoft Excel, allows you to fit a label or text within a single cell and display it on multiple lines. By enabling this feature, the text will automatically wrap within the cell boundaries, ensuring that all the content is visible without overflowing into adjacent cells.
2. To apply the "Wrap Text" command, you can select the cell or cells containing the label, right-click, and choose the "Format Cells" option. In the Format Cells dialog box, navigate to the "Alignment" tab and check the "Wrap text" checkbox. Alternatively, you can find the "Wrap Text" button in the toolbar of the spreadsheet software.
3. In Excel, functions are used to perform calculations or operations on specific data ranges or values. The "SUM" function, in this case, calculates the sum of the values within the range B2 to B6.
4. In the function "=SUM(B2:B6)", "SUM" is the function itself, indicating that we want to calculate the sum. "B2:B6" represents the range of cells from B2 to B6, specifying the data to be summed. The function takes this range as its argument and performs the necessary calculation.
The correct question should be:
1. Which of the following commands lets you display a label on multiple lines within a cell
A. Split
B. Merge & Center
C. Wrap Text
D. Format Painter
2. In the function =SUM(B2:B6), which part of the function is the argument?
A. SUM
B. B2
C. B6
D. B2:B6
To learn more about wrap text visit :
https://brainly.com/question/32265831?
#SPJ11
What information need not be included in a test detect repor?
Answers
In a test detect report, only relevant information should be included. Therefore, any information that is not directly related to the test or the purpose of the report need not be included.
This may include personal or irrelevant information about the individual being tested, unrelated medical history, or unrelated personal history. It is important to focus on the information that is necessary to provide a comprehensive and accurate report, rather than including extraneous information that may detract from the main purpose of the report. When preparing a test detect report, it is essential to include all relevant information that may impact the results of the test. This includes information about the individual being tested, such as their medical history, current medications, and any previous test results. Additionally, it may be necessary to include information about the specific test being performed, including the method used, the equipment used, and any special considerations that may have affected the results.
However, it is equally important to exclude any information that is not relevant to the test or the purpose of the report. This may include personal information about the individual being tested that is not directly related to the test, such as their occupation or hobbies. It may also include irrelevant medical history, such as information about previous illnesses or injuries that are not related to the test being performed. Additionally, it is important to avoid including any information that may be sensitive or confidential, such as information about an individual's mental health or personal relationships. Any such information should be treated with the utmost discretion and only included if it is directly relevant to the test or the purpose of the report. Ultimately, the goal of a test detect report is to provide a comprehensive and accurate assessment of the individual being tested, based solely on the relevant information that pertains to the test. By focusing on the information that is necessary to achieve this goal, it is possible to create a report that is both informative and
To know more about detect report visit:
https://brainly.com/question/32325073
#SPJ11
Question 19 Which of the following statements is true about the the dynamic programming (DP) algorithm for the knapsack problem (P Of the calculation of f) and x) for each pair of/ and a required O),
Answers
The technique of dynamic programming is utilized in solving the knapsack problem by creating a comprehensive table that displays the highest possible profit gained from selecting a particular group of items.
How can this be done?The process of filling up the table begins with an empty set and is sequentially carried out until it reaches the set comprising all the available items.
The DP algorithm's time complexity can be expressed as O(n * W), with n representing the quantity of items and W representing the knapsack's maximum capacity.
Read more about dynamic programming here:
https://brainly.com/question/14975027
#SPJ4